In today’s digital landscape, all business increasingly rely on IT systems for their daily operations, from customer management to financial transactions. Yet, many businesses operate without a formal IT policy, leaving them vulnerable to security threats, compliance risks, and operational inefficiencies. Implementing a well-structured IT policy helps SMEs protect sensitive data, improve cybersecurity, ensure compliance, and set clear expectations for employees using company technology.
Why your SME needs an IT policy
1. Protecting business and customer data
Data breaches and cyberattacks are no longer concerns just for large corporations. SMEs are increasingly targeted by cybercriminals due to their often limited security measures. According to the Belgian Centre for Cybersecurity (CCB), small businesses face particular risks because they typically lack dedicated IT security staff.
A strong IT policy helps protect business-sensitive and customer data by establishing guidelines on:
- Secure password management and multi-factor authentication
- Data encryption and secure storage practices
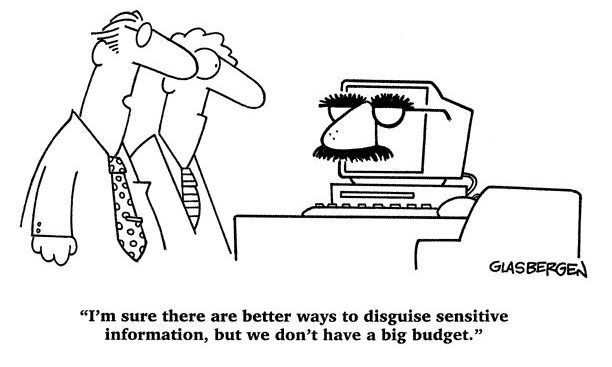
- Access control for sensitive information
- Clear procedures for handling data breaches
- Specific measures for protecting consumer data
Businesses handling sensitive customer information must comply with both GDPR and the Belgian Data Protection Act. Your IT policy should reflect these requirements while remaining practical for daily operations.
2. Ensuring compliance with Belgian and EU regulations
Belgian SMEs face a complex regulatory landscape when it comes to IT security and data protection:
- GDPR Compliance: As an EU member state, Belgian businesses must comply with GDPR requirements
- Belgian Data Protection Act: National legislation that supplements GDPR
- NIS Legislation: Applies to essential service providers
- Industry-Specific Regulations: Additional requirements for sectors like healthcare, finance, and legal services
Your IT policy must address these specific regulatory requirements:
- Appointment of a Data Protection Officer (DPO) when required
- Documentation of data processing activities
- Implementation of appropriate technical and organisational measures
- Regular security assessments and updates
- Procedures for mandatory breach notifications to the Belgian Data Protection Authority
3. Preventing cybersecurity threats
Recent statistics from the CCB show that Belgian SMEs face increasing cyber threats, including:
- Phishing attacks targeting Belgian business email accounts
- Ransomware specifically targeting Belgian accounting software
- Social engineering attacks exploiting Belgian business practices
- Supply chain attacks through Belgian business networks
Your IT policy should include:
- Guidelines for identifying and reporting suspicious emails, particularly those impersonating Belgian authorities or business partners
- Protocols for secure remote work, which became crucial during COVID-19
- Rules for safe internet browsing and email use
- Software and hardware security requirements
- BYOD policies
- Incident response plans that comply with Belgian and European notification requirements
4. Improving operational efficiency and reducing IT downtime
Technology disruptions can significantly impact SMEs. A comprehensive IT policy establishes best practices for:
- Management of IT assets and resources
- Software licensing and update procedures
- Data backup and recovery protocols
- IT support and maintenance schedules
- Integration with Belgian e-government services
- Digital signature and electronic invoicing procedures
5. Setting clear expectations for employees
Belgian labor law requires clear communication of workplace policies. Your IT policy should establish:
- Rights and responsibilities regarding IT usage
- Guidelines for professional email communication
- Prohibited activities (e.g., downloading unauthorized software, accessing unsafe websites)
- Procedures for reporting IT issues
- Training requirements for cybersecurity awareness
How to write an IT policy for your SME
Creating an effective IT policy involves defining key rules and procedures tailored to your SME’s needs.
Step 1: Define the purpose and scope
Begin by outlining the objective of your IT policy. Ask yourself:
- What risks and challenges is this policy addressing?
- Who does the policy apply to? (Employees, contractors, partners, etc.)
- What areas will it cover? (Device usage, cybersecurity, compliance, etc.)
Clearly state the scope of the policy so employees understand its importance and applicability.
Step 2: Outline security and compliance requirements
Include security measures such as:
- Password policies: Minimum password length, complexity, update frequency and use of MFA (Multi Factor Authentication)
- Device security: Antivirus software, firewalls, encryption for company devices
- Data protection: How personal and company data should be handled, stored, and shared
- Compliance measures: Industry regulations like GDPR or sector-specific standards
Employees should know their responsibilities for keeping company and client data secure.
Step 3: Set acceptable sse guidelines
Specify how employees can and cannot use company IT resources:
- Approved devices and applications for work
- Remove work security requirements
- Clous service usage
- Email and internet policies
- Personal device (BYOD) usage rules
- Prohibited activities (e.g., illegal downloads and software, …)
Clarifying acceptable usage prevents misuse of company technology.
Step 4: Establish incident response and support procedures
Clearly define what employees should do in case of IT security issues:
- How to report phishing emails, malware, or data breaches
- Who to contact for IT support (internal IT team or external provider)
- Steps to follow for lost or stolen devices
Create detailed response plans for:
- Data breach detection and reporting
- Ransomware attacks
- Phishing attempts
- Lost or stolen devices
- System outages
- Network security incidents
Having a defined incident response plan ensures quick resolution of IT issues.
Step 5: Implement and communicate the policy
Once drafted, ensure all employees are aware of the IT policy by:
- Holding training sessions and Q&A meetings
- Making the document easily accessible (e.g., company intranet, printed handbook)
- Having employees sign an acknowledgment stating they understand and agree to follow the policy
Regular policy reviews and updates should be scheduled to keep up with evolving cyber threats and technology trends.
Conclusion
A well-crafted IT policy is essential for SMEs to protect their digital assets, ensure regulatory compliance, and maintain efficient operations. By implementing clear guidelines that address both general IT security needs and specific Belgian and/or European requirements, your business can better protect itself against cyber threats while supporting productive operations.
Regular review and updates of your IT policy ensure it remains relevant as technology evolves and new threats emerge. If your business needs assistance developing or updating its IT policy, consider consulting with IT security professionals familiar with the Belgian business environment.
Remember: Your IT policy should be a living document that evolves with your business needs and the changing digital landscape. Regular reviews and updates are essential to maintain its effectiveness and relevance.



